I remember staring at a Wireshark trace at 3 AM, trying to figure out why a critical microservice was dropping connections to our PostgreSQL database. The application logs screamed about TCP timeouts, but the PCAP file I pulled from the core switch’s SPAN port looked perfectly clean. No retransmissions, no RST packets, no malformed headers. Just absolute silence during the exact window the outage occurred.
It took me three hours and a lot of caffeine to realize the switch itself was lying to me. The switch’s CPU had spiked to 95% due to a routing loop, and because port mirroring is the lowest priority task on a switch ASIC, it simply stopped copying the mirrored packets to my capture tool. The production traffic was still flowing (and failing), but my visibility was completely severed. That night burned a harsh lesson into my brain about the fundamental differences in network architecture and visibility.
If you’re building a network infrastructure, deploying intrusion detection systems (IDS) like Suricata or Zeek, or just trying to track down a ghost in the machine, you will inevitably face the port mirroring vs network tap debate. Both methods extract packets from your production network and feed them into your security and network monitoring tools, but they do it in vastly different ways. Relying on the wrong one will leave you blind when you need visibility the most. Let’s break down exactly how these two approaches work, where they fail, and which one you should deploy in your production environments.
What is Port Mirroring (SPAN)?
Port mirroring, most commonly known in the Cisco world as SPAN (Switched Port Analyzer), is a software feature built into the operating system of a network switch. It instructs the switch’s forwarding ASIC to take a copy of every packet entering or exiting a specific port (or VLAN) and send that copy to a designated destination port where your packet analyzer or IDS is waiting.
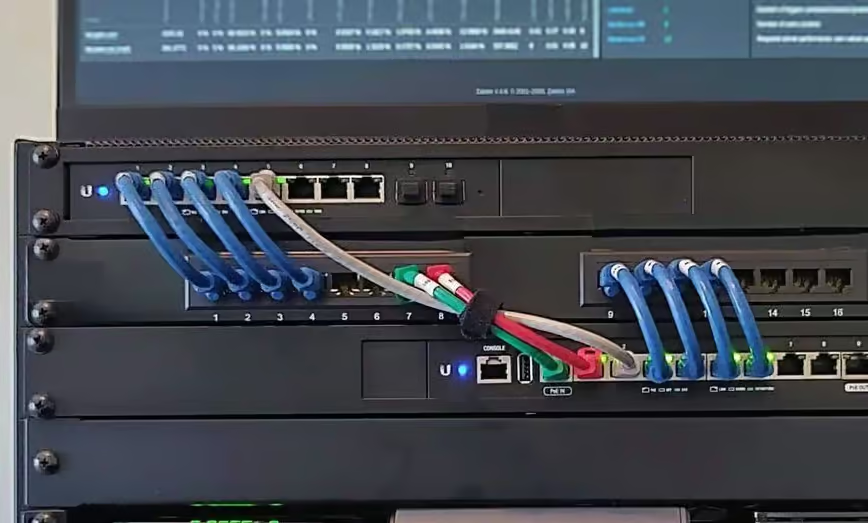
Because it’s built directly into the switch, you don’t need to buy additional hardware to use it. If you have a managed switch from Cisco, Juniper, Arista, or even a prosumer Ubiquiti device, you already have port mirroring capabilities.
Configuring Port Mirroring in the Real World
Setting up a local SPAN session is trivial. Here is what it looks like on a standard Cisco Nexus or Catalyst switch. In this scenario, we want to monitor traffic on GigabitEthernet1/0/1 and send the copy to our Wireshark laptop plugged into GigabitEthernet1/0/24:
# Enter global configuration mode
configure terminal
# Define the source port and direction (both transmit and receive)
monitor session 1 source interface GigabitEthernet1/0/1 both
# Define the destination port
monitor session 1 destination interface GigabitEthernet1/0/24
# Verify the configuration
show monitor session 1
There are also advanced variations like RSPAN (Remote SPAN), which sends mirrored traffic across multiple switches via a dedicated VLAN, and ERSPAN (Encapsulated Remote SPAN), which wraps the mirrored packets in a GRE (Generic Routing Encapsulation) tunnel. ERSPAN is incredibly powerful for cloud networking and DevOps teams because you can mirror traffic from a physical switch in a datacenter directly to a Linux VM running in AWS or Azure.
If you are receiving ERSPAN traffic on a Linux server (say, an Ubuntu box running Zeek for network security), you need to decapsulate that GRE tunnel. Here is exactly how you configure the Linux network stack to receive ERSPAN traffic:
# Load the GRE kernel module
sudo modprobe ip_gre
# Create an ERSPAN tunnel interface monitoring traffic from the switch IP (10.0.0.5)
sudo ip link add dev erspan0 type erspan local 192.168.1.10 remote 10.0.0.5 seq key 10
# Bring the interface up
sudo ip link set dev erspan0 up
# Verify traffic is arriving using tcpdump
sudo tcpdump -i erspan0 -n
The Flaws of Port Mirroring: Why SPAN Drops Packets
While port mirroring is free and flexible, it comes with severe architectural flaws that make it unsuitable for high-fidelity network security or forensics.
First, SPAN is a low-priority process. Switch ASICs are designed to route and switch production traffic as fast as possible. If the backplane becomes congested, or if the CPU spikes, the switch will silently drop the mirrored packets to preserve resources for production traffic. You will never get an alert that packets were dropped; your capture will just have missing frames.
Second, the oversubscription math guarantees packet loss. Network links are full-duplex. A 10Gbps link can simultaneously transmit 10Gbps and receive 10Gbps, meaning there is actually 20Gbps of potential traffic on that wire. If you mirror both the RX and TX of that 10Gbps link to a single 10Gbps destination port, what happens when the source link hits 60% utilization? You are trying to shove 12Gbps of mirrored traffic out of a 10Gbps port. The switch’s buffers will fill up in milliseconds, and it will aggressively drop the excess packets. If you are feeding an IDS, those dropped packets could contain the exact malicious payload you were trying to detect.
What is a Network TAP?
A Network TAP (Test Access Point) is a purpose-built hardware device inserted physically inline between two network devices—for example, between your edge router and your core firewall. Unlike port mirroring, which relies on software and CPU cycles, a TAP is a completely passive hardware layer device.
When you install a TAP, you unplug the cable connecting your router and firewall, plug both ends into the TAP’s network ports, and then connect your monitoring tools to the TAP’s monitor ports.
How a TAP Physically Works
The beauty of a TAP lies in its physical simplicity. In fiber optic networks, a passive optical TAP doesn’t even require electricity. It uses internal glass prisms to physically split the light beam. A common split ratio is 70/30, meaning 70% of the light continues to the production network, and 30% of the light is redirected to the monitoring port. Because it’s literally just bending light, an optical TAP introduces zero latency, cannot be hacked, and cannot drop packets due to CPU load.
Copper TAPs (for standard twisted-pair Ethernet cables like Cat6) do require power to duplicate the electrical signals, but they utilize fail-to-wire technology. If the TAP loses power or suffers a hardware failure, internal mechanical relays instantly snap shut, physically bridging the connection between the two network devices. The network experiences a brief microsecond flutter, and production traffic continues flowing uninterrupted.
Why TAPs are the Gold Standard for Packet Capture
I absolutely refuse to deploy enterprise network security tools without using TAPs. The reasons are entirely based on data fidelity at Layer 1 and Layer 2 of the OSI model.
When an Ethernet frame hits a switch port, the switch checks the Frame Check Sequence (FCS) to ensure the packet isn’t corrupted. It also checks for layer 1 errors like runts (frames smaller than 64 bytes) or giants (frames larger than 1518 bytes). If a switch receives a corrupted frame, it immediately discards it. A SPAN port will never see these corrupted packets because the switch drops them before the mirroring process even begins.
A network TAP, however, copies everything on the wire exactly as it exists. If a failing Network Interface Card (NIC) is spewing malformed, corrupted frames onto your network and causing a broadcast storm, a TAP will capture those exact corrupted frames, allowing you to easily identify the hardware failure in Wireshark. A SPAN port would just show you a frustratingly empty screen.
Port Mirroring vs Network TAP: The Technical Breakdown
To really understand the port mirroring vs network tap comparison, we have to look at how they stack up across performance, security, and deployment complexity.
1. Performance and Timing Precision
If you work in High-Frequency Trading (HFT) or low-latency telecom environments, timing is everything. When you analyze a PCAP file, you rely on the timestamps applied to each packet. When a switch mirrors a packet via SPAN, the timestamp is applied after the packet has traversed the switch’s internal buffers and queues. This introduces microsecond-level jitter. You cannot accurately measure network latency using a SPAN port because the mirroring process itself alters the timing.
A TAP operates at wire speed. When combined with a high-end capture card (like a Napatech or Endace card), you get highly precise, hardware-stamped nanosecond resolution. You see the exact moment the electrical signal hit the wire.
2. Security and Forensic Integrity
In a court of law, digital forensics evidence must be demonstrably tamper-proof. SPAN ports fail this test. Because SPAN is a software configuration, a compromised switch could be reconfigured by an attacker to stop mirroring their malicious traffic. Furthermore, SPAN destination ports can theoretically be configured to transmit traffic back into the network, meaning an attacker who compromises your IDS could pivot back into your core network.
TAPs are strictly unidirectional. The monitoring ports physically lack the transmit (TX) lines required to send data back into the production network. It is physically impossible for traffic to flow from the monitoring tool back into the network. This provides an absolute, hardware-enforced security boundary that compliance auditors love.
3. Cost and Deployment Complexity
This is the one area where SPAN unequivocally wins. SPAN is free. It takes thirty seconds to configure via SSH, and you can tear it down just as fast. If I’m troubleshooting a user’s slow web application, I’m going to use a temporary SPAN session.
TAPs are expensive. A single 10G fiber TAP might cost a few hundred dollars, but managing the output requires dual monitor ports (one for the RX strand, one for the TX strand). To feed both of these strands into a single interface on your Wireshark laptop, you need a Network Packet Broker (NPB) to aggregate the traffic, which can cost tens of thousands of dollars. Furthermore, installing a TAP requires bringing the link down to physically insert the device, meaning you have to schedule a maintenance window.
Real-World Scenarios: When to Use Which
Choosing between port mirroring and a network TAP isn’t about finding a singular “best” technology; it’s about applying the right tool to the right architectural problem.
Scenario 1: Day-to-Day DevOps Troubleshooting (Winner: SPAN)
Imagine your Kubernetes cluster is occasionally failing to resolve external DNS queries. You need to see the UDP port 53 traffic leaving your worker nodes. You don’t need 100% forensic perfection; you just need to see if the DNS server is sending NXDOMAIN responses or dropping the queries entirely.
In this case, configuring a quick SPAN session on the top-of-rack switch and dumping the traffic into tcpdump is the perfect solution. It requires zero budget, zero downtime, and provides immediate answers.

Scenario 2: Deploying an Enterprise IDS/IPS (Winner: Network TAP)
You are deploying Suricata at your network perimeter to detect malware signatures and command-and-control (C2) traffic. Your internet edge is passing 5Gbps of sustained traffic.
If you use a SPAN port, a sudden microburst of traffic (say, an unexpected backup job triggering) will cause the switch to drop the mirrored packets. If the malware payload happens to traverse the switch during that microburst, your IDS will not see the attack. Your multi-million dollar security stack is rendered useless by a switch buffer. In this scenario, a physical TAP is mandatory. You must guarantee that every single packet reaches the IDS engine.
Scenario 3: Cloud Networking and SDN (Winner: ERSPAN / VPC Mirroring)
If your infrastructure is entirely hosted in AWS, GCP, or Azure, you cannot install a physical TAP. You don’t own the hardware. In cloud networking, you must rely on cloud-native mirroring features like AWS VPC Traffic Mirroring. Under the hood, this functions identically to ERSPAN, encapsulating the virtual network traffic and sending it to an elastic network interface (ENI) on your monitoring instances. Software-Defined Networking (SDN) relies entirely on software-based mirroring.
Aggregating the Chaos: Network Packet Brokers (NPBs)
As your network scales, you will realize that neither TAPs nor SPAN ports scale easily on their own. If you have 50 TAPs deployed across your datacenter, you don’t want to buy 50 separate IDS appliances. This is where Network Packet Brokers (NPBs) come into play.
Devices from vendors like Gigamon, Ixia (Keysight), or Arista (DANZ) act as massive aggregators. You cable all of your network TAPs and SPAN ports into the NPB. The NPB then deduplicates the traffic, decrypts HTTPS payloads, filters out irrelevant traffic (like Netflix or YouTube video streams), and distributes the clean, optimized packet streams to your various security and monitoring tools.
By placing an NPB between your TAPs and your tools, you offload the heavy lifting. Your Suricata box doesn’t have to waste CPU cycles dropping encrypted video packets; it only receives the exact HTTP, DNS, and TCP handshake data it needs to analyze.
Frequently Asked Questions (FAQ)
What is the difference between SPAN and TAP?
SPAN (port mirroring) is a software feature on a network switch that copies traffic to a monitoring port, which can cause CPU strain and dropped packets. A network TAP is a physical hardware device installed inline on the network cable that passively copies 100% of the traffic without affecting network performance or dropping frames.
Can a network TAP cause an outage?
Installing a TAP requires briefly disconnecting the network cable, which causes a momentary outage. However, once installed, modern copper TAPs use fail-to-wire relays, and optical TAPs use passive glass prisms, ensuring that even if the TAP loses power, the production network traffic continues to flow uninterrupted.
Does port mirroring affect network performance?
Yes, port mirroring can negatively impact a switch’s performance. Copying packets consumes CPU cycles and backplane bandwidth. If the switch becomes heavily loaded, it will prioritize routing production traffic and will silently drop the mirrored packets to protect the network’s core functions.
Can I use port mirroring for a firewall?
Port mirroring is only suitable for passive monitoring tools like Intrusion Detection Systems (IDS) or packet analyzers (Wireshark). Because mirrored traffic is a copy of the data that has already passed through the switch, you cannot use a SPAN port to feed an active, inline firewall that needs to block traffic in real-time.
Conclusion
The port mirroring vs network tap debate ultimately boils down to a trade-off between convenience and fidelity. Port mirroring is an incredible tool for on-the-fly network troubleshooting, temporary packet captures, and environments where budget is non-existent. However, its architectural limitations—specifically packet dropping under load and the inability to capture physical layer errors—make it a massive liability for enterprise security.
If you are deploying compliance-driven forensics tools, intrusion detection systems, or network performance monitors that require absolute precision, you must invest in physical Network TAPs. By combining passive TAPs at your network perimeter with a robust Network Packet Broker to filter and aggregate the data, you build a monitoring architecture that provides 100% visibility without ever compromising the stability of your production network.